from Kalcifer@sh.itjust.works to cybersecurity@sh.itjust.works on 30 May 2024 06:46
https://sh.itjust.works/post/20092774
The article says the following:
Linux 6.10 is introducing support for Trusted Platform Module (TPM2) encryption and integrity protections to prevent active/passive interposers from compromising them. This follows a recent security demonstration of TPM key recovery from Microsoft Windows BitLocker being demonstrated. TPM sniffing attacks have also been demonstrated against Linux systems too, thus the additional protections be made with Linux 6.10 to better secure TPM2 modules.
I’m a little confused with this article. Is it talking about implementing TPM parameter encryption? If so, does this mean that the TPM bus prior to kernel v6.10 was unencrypted? Will this kernel feature still require a patch to be made to software like systemd-cryptenroll? Are the sniffing attacks that it’s talking about examples of MITM attacks like this? Does windows encrypt the TPM bus?
threaded - newest
This is the best summary I could come up with:
Linux 6.10 is introducing support for Trusted Platform Module (TPM2) encryption and integrity protections to prevent active/passive interposers from compromising them.
The TPM device driver changes were already mailed into Linus Torvalds for the Linux 6.10 merge window.
The Linux 6.9 stable kernel is expected on Sunday and thus in turn the opening of the v6.10 merge window.
The TPM device driver code is rolling out Trusted Platform Module bus encryption and integrity protection.
The key-pair on the TPM side is generated from a null random seed on a per-power-on basis of the system.
These additional protections are deemed necessary for the physical security of the system given the recent TPM bus interposer attacks that have been demonstrated.
The original article contains 188 words, the summary contains 118 words. Saved 37%. I’m a bot and I’m open source!
AFAIK Windows is also prone to this. TPM bus is not encrypted on Windows too and you can break into bitlocker protected laptop. Video Source
By chance, do you have an official source from Microsoft that states that? I was unable to find any official documentation to clarify that when I looked.
This video that you linked is the same video that I linked close to the end of my post.
Lol! Didn’t check the source. I remembered watching this video a month ago, So I linked it.
After researching more this is the information I found.
This type of attack is only possible with external TPM without PIN protection. (Not a problem for fairly new CPUs with integrated TPM ~5 year old.) This method of breaking into bitlocker isn’t new. A hijaker demonstrated it back in 2013
Source.
So, the Linux kernel feature will improve TPM security for older computers
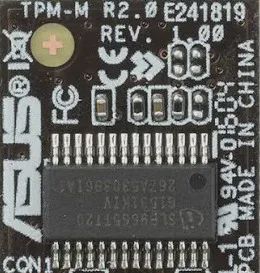
TPMs have been able to store encryption keys instead of having them stored on disk or embedded inside software. But TPMs were mostly connected to the main system via simple buses like I2C, SPI, or simple UART. People figured out that by sticking a cheap sniffer like the ChipWhisperer, it would be easy to read off those keys while in transit.
Even easier would be to MITM using methods like clock glitching, so they would return fake credentials and get access to everything.
The next generation TPMs allowed on-device private/public key creation using creative random number generation schemes and on-board crypto libraries that couldn’t be tampered with. But there was still the problem of keys going across those open busses.
To solve this problem, you need to have attestations between the main board and TPM which means storing multiple public keys and digital signatures from both sides, either during manufacturing or on first boot.
This way, if someone sniffs the wires, the data stream is asymmetrically encrypted. And with attestation, each side knows they are talking to only the right sender and receiver. Also, no two systems will have a common key, so even if someone de-caps a TPM2 module and gets the keys out, they can’t use it to compromise other devices.
This is where we’re at. Manufacturing and boot processes have to be modified to make sure nothing leaks out and everything stays put.
Meaning that software like systemd-crytpenroll would need to be updated to support this? I suppose what I’m trying to ask is this: As a user, if I want to set up full disk encryption using a TPM (1.2 or 2.0?) module, would I need to do anything different/novel during installation if I wanted to ensure that the bus is encrypted? And, if so, what would I need to do?