from 0x815@feddit.de to technology@beehaw.org on 05 Jun 2024 15:33
https://feddit.de/post/12852643
Here is the report (pdf) — (archived report)
- An unnamed high-profile government organization in Southeast Asia emerged as the target of a “complex, long-running” Chinese state-sponsored cyber espionage operation codenamed Crimson Palace.
- The name of the government organization was not disclosed, but the company said the country is known to have repeated conflict with China over territory in the South China Sea, raising the possibility that it may be the Philippines.
- China’s cyber threat activity outpaces other nation-state cyber threats in volume, sophistication and the breadth of targeting, accordi.g to experts, calling out their use of compromised small office and home office (SOHO) routers and living-off-the-land techniques to conduct cyber threat activity and avoid detection.–
“The overall goal behind the campaign was to maintain access to the target network for cyberespionage in support of Chinese state interests,” Sophos researchers Paul Jaramillo, Morgan Demboski, Sean Gallagher, and Mark Parsons said in a report shared with The Hacker News.
“This includes accessing critical IT systems, performing reconnaissance of specific users, collecting sensitive military and technical information, and deploying various malware implants for command-and-control (C2) communications.”
The name of the government organization was not disclosed, but the company said the country is known to have repeated conflict with China over territory in the South China Sea, raising the possibility that it may be the Philippines, which has been targeted by Chinese state-sponsored groups like Mustang Panda in the past.
Crimson Palace comprises three intrusion clusters, some of which share the same tactics, although there is evidence of older activity dating back to March 2022 -
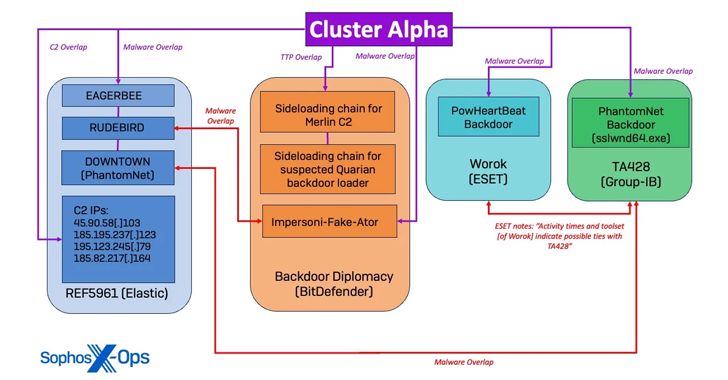
- Cluster Alpha (March 2023 - August 2023), which exhibits some degree of similarity with actors tracked as BackdoorDiplomacy, REF5961, Worok, and TA428
- Cluster Bravo (March 2023), which has commonalities with Unfading Sea Haze, and
- Cluster Charlie (March 2023 - April 2024), which has overlaps with Earth Longzhi, a subgroup within APT41
Sophos assessed that these overlapping activity clusters were likely part of a coordinated campaign orchestrated under the direction of a single organization.
The attack is notable for the use of undocumented malware like PocoProxy as well as an updated version of EAGERBEE, alongside other known malware families like NUPAKAGE, PowHeartBeat, RUDEBIRD, DOWNTOWN (PhantomNet), and EtherealGh0st (aka CCoreDoor).
Other hallmarks of the campaign include the extensive use of DLL side-loading and unusual tactics to stay under the radar.
“The threat actors leveraged many novel evasion techniques, such as overwriting DLL in memory to unhook the Sophos AV agent process from the kernel, abusing AV software for sideloading, and using various techniques to test the most efficient and evasive methods of executing their payloads,” the researchers said.
Further investigation has revealed that Cluster Alpha focused towards mapping server subnets, enumerating administrator accounts, and conducting reconnaissance on Active Directory infrastructure, with Cluster Bravo prioritizing the use of valid accounts for lateral movement and dropping EtherealGh0st.
Activity associated with Cluster Charlie, which took place for the longest period, entailed the use of PocoProxy to establish persistence on compromised systems and the deployment of HUI Loader, a custom loader used by several China-nexus actors, to deliver Cobalt Strike.
“The observed clusters reflect the operations of two or more distinct actors working in tandem with shared objectives,” the researchers noted. “The observed clusters reflect the work of a single group with a large array of tools, diverse infrastructure, and multiple operators.”
The disclosure comes as cybersecurity firm Yoroi detailed attacks orchestrated by the APT41 actor (aka Brass Typhoon, HOODOO, and Winnti) targeting organizations in Italy with a variant of the PlugX (aka Destroy RAT and Korplug) malware known as KEYPLUG.
“Written in C++ and active since at least June 2021, KEYPLUG has variants for both Windows and Linux platforms,” Yoroi said. “It supports multiple network protocols for command and control (C2) traffic, including HTTP, TCP, KCP over UDP, and WSS, making it a potent tool in APT41’s cyber-attack arsenal.”
It also follows an advisory from the Canadian Centre for Cyber Security warning of increasing attacks from Chinese state-backed hacking aimed at infiltrating government, critical infrastructure, and research and development sectors.
“[People’s Republic of China] cyber threat activity outpaces other nation-state cyber threats in volume, sophistication and the breadth of targeting,” the agency said, calling out their use of compromised small office and home office (SOHO) routers and living-off-the-land techniques to conduct cyber threat activity and avoid detection.
threaded - newest